
INTERNET GOTCHAS
CYBERSECURITY TRAINING
It’s easy to become the unwitting victim of the so-called “dark UX patterns” found on everyday websites across the Internet. When cybersecurity is critical (and, of course, it always is) falling for these design tricks can have real consequences for employees, clients, and companies. This course bypasses a “telling” approach, and asks the viewer to do some thinking for themselves.
THIS PROGRAM'S SPECIAL POWERS
Must-know information
To avoid the usual cybersecurity snoozefest, this program delivers must-know information in a simple, straightforward way, then immediately releases the viewer to work with the information in their own way.

Designed to engage
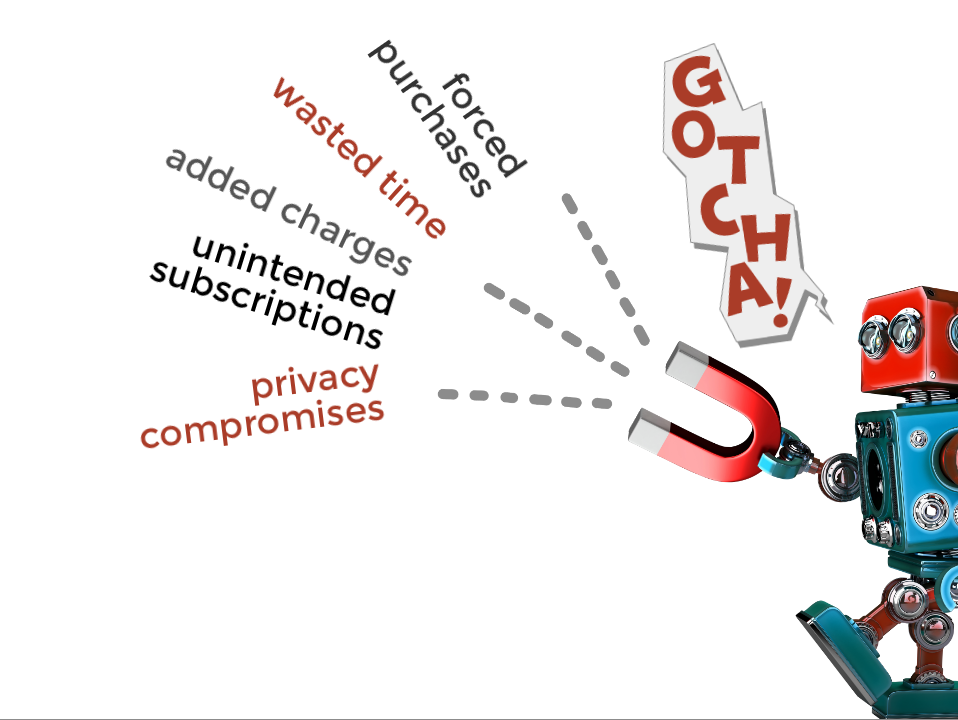
Cybersecurity programs discuss concepts that are not always easy to show graphically. In this program, the concepts take on a personality that seems, well, almost human.
Truly personalized learning
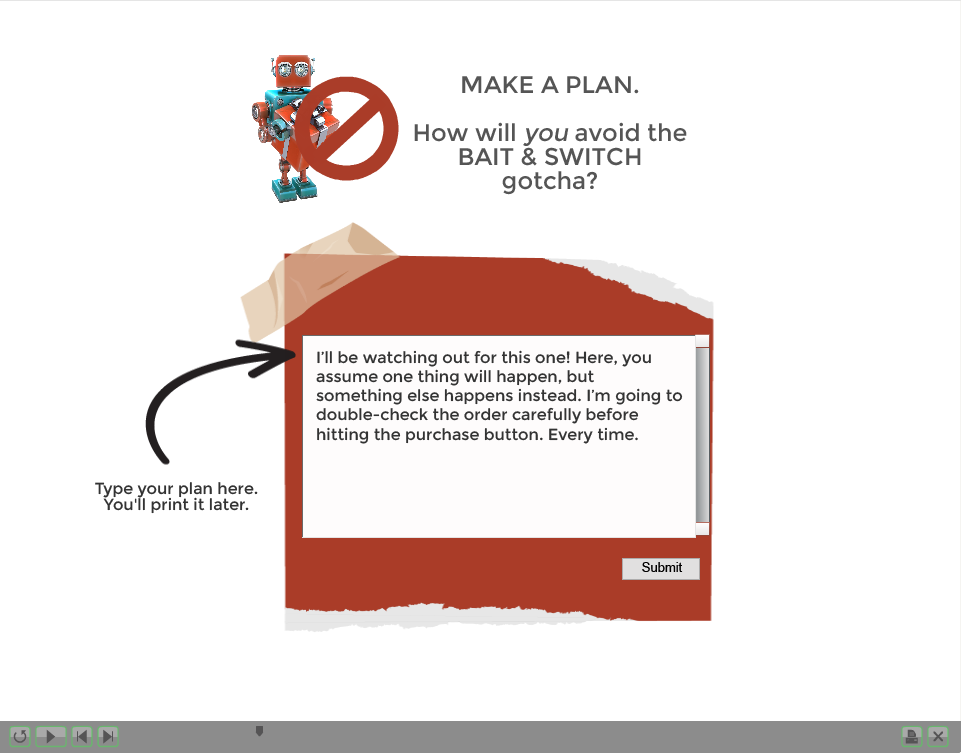
Elearning programs are often self-contained units, running more like videos than interactive learning experiences. Using a simple setting available in Adobe Captivate, this program breaks that barrier, asking the viewer to develop and record their own printable work aid.
DEVELOPMENT NOTES
Challenges
For the average computer user, what is most important, need-to-know information to avoid cybersecurity breakdowns? Usually, it’s not the technical details! Instead, it’s awareness, an eyes-wide-open approach to what’s happening on-screen.Tell someone to pay attention, and they may or may not do so.
Strategies
Instead of delivering a barrage of cybersecurity factoids and must-dos that won’t be remembered in the moments when the information counts, ask the viewer to stop, think, and make a plan by themselves and for themselves.
Solution
This program does just that. It keeps the content light and relevant, and delivers a portion of the content non-verbally with the use of human-like robot “characters.” At important moments the viewer is asked to record their own insights into fillable forms. Later in the program, these are gathered together into a printable, viewer-built work aid.

